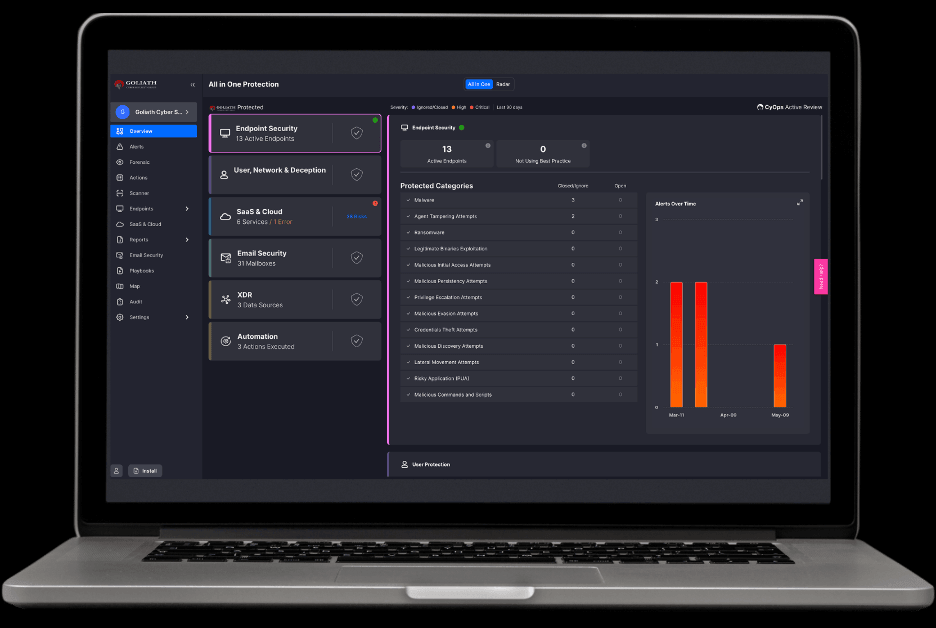
Unified.
AI-Powered.
24×7 Expert Backed.
Enterprise Grade Protection.
Made Simple!

INDUSTRY TRUSTED, CUSTOMER LOVED.

2025 MITRE ATT&CK Evaluations
100% Detection Visibility
100% Technique-Level Coverage
100% Protection
ZERO – False Positives
ZERO – Configuration Changes
Top-Tier Performance
according to our users
98% score for Real-Time Detection
97% score for 24/7 support
97% score for Automated Remediation

Recommended by 95%
4.8/5 Overall Rating
4.8/5 Product Capabilities Rating
4.8/5 Ease of Deployment Rating
Goliath 360 Program Packages
Modern Security Demands a Unified Platform
Today’s threats move faster than most teams can react. Disconnected tools create blind spots, slow response, and higher costs. Goliath 360 fixes that.
By unifying protection, detection, and response in a single unified AI-Powered platform, the Goliath 360 program helps you stay ahead of every threat while simplifying security.
GOLIATH 360 – PROTECT
- MITRE ATT@CK Integration
- NextGen Antivirus
- Threat Intelligence, Ransomware & Malware Protection
- Exploit & Critical OS Component Protection
- Credential, Files & Document Protection
- Device Control
- End User Controls & Dashboard
- Windows Event Visibility
- Network, File & Process Event Visibility
- Application & Endpoint Visibility
- Threat Hunting
- Forensic & Automated Investigations
- Custom Detection Policies
- Send To Sandbox
- Automated Investigation & Remediation
- Secure Remote Shell
- Endpoint Misconfiguration Detection & Remediation
- Detect Vulnerable Apps Across Endpoints (CVE)
- Device, Network, Apps & Phishing Threat Detection
- On-Device Remediation
- Mobile App Risk Detection & Mitigation
- iOS, Android & Chrome OS Devices
- Network Scan Detection
- Network Poisoning Detection
- Tunnel Exfiltration Detection
- Domain Filtering
- External Attack Surface Management / Port Scan
Unifies identity, cloud, and endpoint defenses in one platform, delivering instant detection and automated response that log-only systems can’t match.
Enables you to create precise, category-based web filtering policies for enhanced control over internet access. You can configure which categories to track or block, directly from the UI.
- User Activity Visibility
- Lateral Movement Detection
- Deceptive Users
- High & Critical threats are identified and addressed
- Deceptive Endpoints & Servers
- Deceptive Files & Documents
- Deceptive Users
- Integration With Office 365 & Google Workspace
- Phishing & Malware E-mail Detection & Remediation
- Unauthorized Senders Management
- Safe URL’s
- Security Misconfiguration Detection & Remediation
- Compliance Management
- Notification & Reports
- Cloud Users & Resource Inventory
- Native & 3 rd Party Forensic Data HOT Retention
- Native & 3 rd Party Forensic Data COLD Retention *
- Forensic Investigations Across Data Sources
- Correlated Alerts Across Data Sources (XDR)
* Available as add-on
- Automated Response Actions & Playbooks
- Customized Playbooks
- API & 3 rd Party Integrations *
* See Contract Terms for Limitations and Upgrade Options
GOLIATH 360 – DEFEND
** INCLUDES EVERYTHING IN PROTECT **
Cybersecurity awareness training program, fully automated with the right amount of personalization.
- Continuous Sync with Your Company Directory (ex: AD)
- Automated Training Assignments
- Guaranteed Email Delivery
- Randomized Phishing Simulations
- Phish Reporting Add-In
- Custom Policy Creation
- Automated Reporting
GOLIATH 360 – SHIELD
** INCLUDES EVERYTHING IN PROTECT & DEFEND **
A 24×7 SOC Service providing world-class security services adding additional layers of protection.
- Full Alert Handling
- Full Alert Investigation
- 1hr Response Handling SLA
- Proactive Threat Hunting & Remediation
- On Demand File Analysis
- Exclusions, Whitelisting & Tuning
- Lighthouse Scans – Credential Theft Monitoring
Additional Cyber Advisory Services
** Optional on ALL Packages **
- Security Program Development
- Risk Management
- Security Architecture & Infrastructure Development
- Vendor Management (Risk Assessments)
- Compliance & Regulatory Requirements (Including Audit Support)
- Security & Awareness Training (Tabletop Exercises)
- Incident Response & Forensics Plan & Response Efforts
- Security & Awareness Training (Tabletop Exercises)
- Security Monitoring & Threat Intelligence
- Leadership & Team Collaboration
Vanquish Human Risk with Cognitive Security.
By analyzing task-level intent, we apply the right policies and protections for the moment. From sensitive research to content generation, adapt safeguards based on use case, not guesswork.
- Start with Shadow AI Assessment
- Expand to Enforcement
- Mature to Cognitive Security
This assessment will simulate an advanced hacking team who is using multiple methods (manual & automated testing) to obtain access into the Customer network. During the assessment, a standardized methodology and framework called the MITRE ATT&CK is utilized to maintain a consistent approach to the testing.
Prepare for CMMC Compliance
We provide the foundation for your compliance with CMMC and a road map to attaining certification.
- Gap analysis
- System Security Plan
- Plan of Action and Milestones (POA&M)
Built for Security. Certified for Compliance.
Meet and maintain compliance with major standards including SOC 2 Type 2, ISO 27001, NIST CSF, HIPAA, PCI DSS, DFARS, CMMC, NIS2, and DORA.
Every capability is designed to strengthen resilience, simplify audits, and prove continuous protection.

