Malware Detection
Malware is indeed the most common cause for endpoints to be compromised. Trojan, worms and botnets are common types of malware that are used by cyber criminal and hackers to infect devices and launch other nefarious activities such as reconnaissance on internal hosts/servers/devices, beaconing with C&C center, establishing backdoors and webshells, spreading out laterally, escalating privilege and so on. Zero-Day malware and Ransomware, known to cause operational and financial havoc across industries, are quite unpredictable and worrisome.
Challenges
- Endpoints outside organizational firewall are often unguarded against malicious websites or torrent-based activities that invite malware.
- Evasive techniques, including obfuscation and stealth mode, makes malware detection quite challenging.
- Evolution of known vectors over time renders futility to previous tried defenses, signatures and heuristic based detection techniques.
Goliath Cyber’s Solution
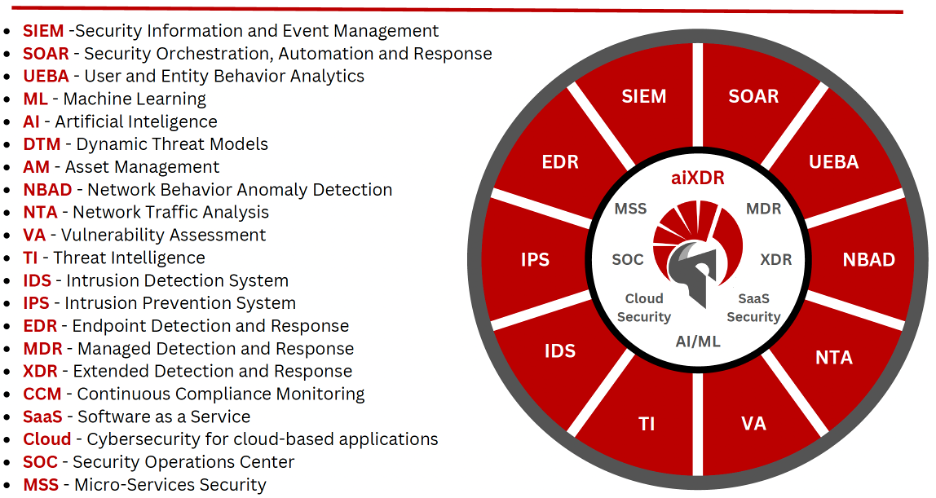
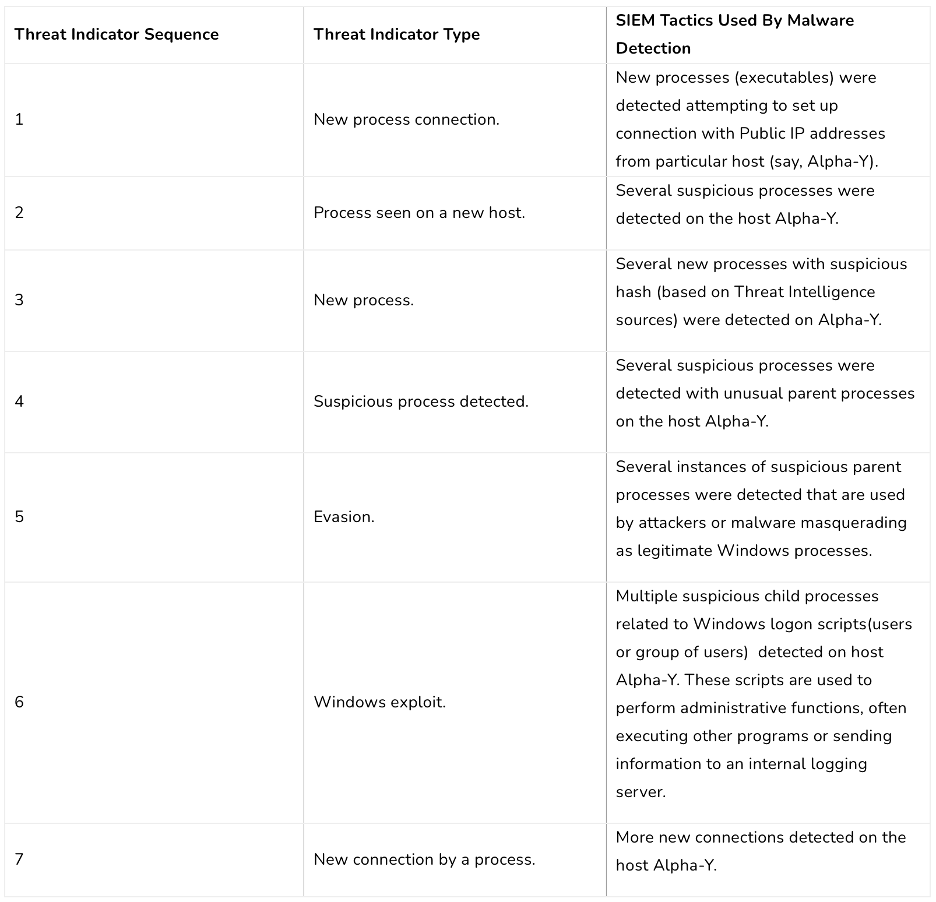
Malware tactics and techniques have evolved to avoid detection by software tools (system maintenance) and security controls (whitelisting/blacklisting). Sophisticated methods (including ML and AI) are used to overcome advanced detection techniques. This leaves very little to guesswork and static rules. Goliath Cyber’s solution (both aiSIEM and aiXDR), however, relies primarily on behavioral patterns across users and entities while questioning suspicious processes, file changes, connections, scans etc, while keeping eyes and ears open to the external world of Cyber Threat Intelligence. This mode of staying on the toes aided by ML and AI imparts aiXDR and aiSIEM the ability to catch Zero-Day Threats, Ransomware and other malware variants with high degree of confidence.
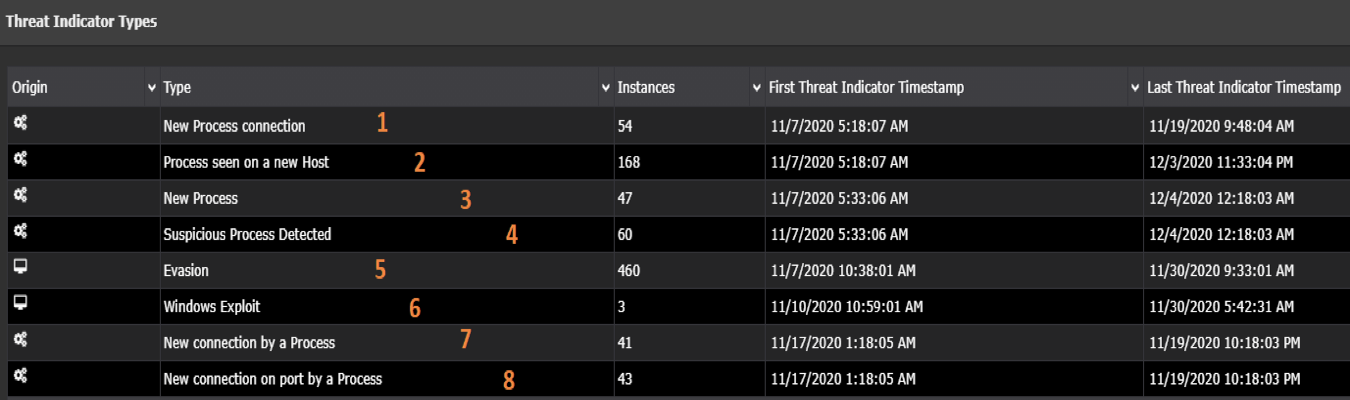
When drilling down, we get a granular picture with different types of Threat Indicators and number of instances associated with each indicator.
Brute Force Attack
In a Brute Force Attack, the adversary tries to guess the username-password combination repeatedly to gain access, without the risk of detection. Reverse Brute Force Attack may be unleashed through Password Spraying where multiple user accounts are sprayed with commonly used passwords such as “password”, “Password123” etc. Also, credentials obtained from dark web are used to hack other accounts that could very possibly be using the same password – a classic case of Credential Stuffing.
Challenges
- Attackers can sneak into a host and launch offline attacks that tend to be more effective but all the more difficult to detect and thwart.
- Lack of security hygiene, particularly for password creation and maintenance, can lead to an easy win for Brute Force Attack.
- Connections to applications and servers without VPN or strong SSL could make it easier for attacker to take advantage of online mode.
Goliath Cyber’s Solution
It is crucial for a solution to presume Zero-Trust and rely on contextual awareness and behavioral Analytics to identify attacks. Goliath Cyber’s solution takes into consideration geo location, IP address, time-of-day, device, login frequency and policy violations, along with anomalous user behavior by the leveraging Machine Learning. Also, the platform looks for signs like new login at the host, new connection and new command to identify a potential case for credential stuffing.
Additional scenarios of Brute Force Attack tracked and detected by Goliath Cyber’s solution (both aiSIEM and aiXDR):
- Large number of failed logins from single/multiple IPs, internal or external, against a single/multiple usernames.
- Failed logins from new geo locations or new user device.
- Large number of Account Lockouts.
- Password spraying brute force attack to breach accounts with simple password.
Goliath Cyber’s solution goes a step further and determines if the attacker has successfully breached the account. Beyond raising alerts, the solution helps eliminate attacks from being successful by pushing policies to the firewalls to block the IP address(s) from where the attacks are originating, or disable the user by pushing the policy to domain controller.

Insider Threat
Insiders within an organization could become threat, advertently or inadvertently, by virtue of their intentions. While accessing private information, business sensitive data and intellectual property (patent, code, blueprint) may or may not be allowed by the role, sharing such information with someone not entitled or copying/forwarding for personal use can cause material and monetary damage to the organization. Besides, there are disgruntled employees who perpetrate malicious acts by stealing credentials, exposing and trading business information or wiping out data and intellectual property.
According to Ponemon Institute Global Report in 2020 (Cost of Insider Threats), the average global cost of insider threats rose by 31% between 2018 and 2020 (reaching $11.45 million) and frequency of incidents increased by 47% at the same time.
Challenges
- Insider behavior is often difficult to ascertain as it conflicts with the trust factor or program requirements.
- Insider threat cannot be pre-determined and controlled through policies due to the ad hoc nature.
- An entitled user accessing business information while on travel or during odd hours may not necessarily imply suspicious activity.
Goliath Cyber’s Solution
Insider threat detection is addressed by Goliath Cyber through User Entity Behavior Analytics (UEBA) riding on Machine Learning algorithms to identify various tactics and techniques used the perpetrators.
- Compromised Credential is a clear indicator of an insider trying to gain access to information that he or she could potentially misuse. As shown in the screenshot below (aiSIEM Portal), a particular user was found to be logging into an unexpected host – which was a departure from profiled behavior.
- Data Exfiltration is also an activity that may be undertaken by the insider. In this case, there may be indicators of increased communication with a high-value host. The techniques applied are similar to Data Breach Detection use case.
In both the scenarios, an alert with major or critical severity would be raised by the platform with suggestive recommendations.

Data Breach
Data Breach (a.k.a Data Exfiltration or Theft) is a primary reason for malefactors to hatch a plan of attack into an organizations digital information that can range from personal data to business sensitive information to intellectual property. Hidden agendas could be tied to financial gains by trading customer information, performance (financial) data, PII, PHI and credit card information in the dark web. Also, motives could be flamed by intent to cause disrepute to a particular organization, business or nation state.
Challenges
- Data Exfiltration is difficult to detect as it mimics normal traffic and can go undetected.
- Traditional solutions (including DLP) generate large volume of false positives that are expensive to manage and impacts user experience, including productivity.
- Typically data exfiltration is detected after a good amount of damage is already done. For example, Equifax took 75 days to detect the breach.
Goliath Cyber’s Solution
Data Breach detection requires analysis of security related data from multiple angles – file usage, user activity and network traffic (applications, servers). Additionally, threat intelligence and vulnerability scan result plays important role in enriching context, particularly when external perpetrators are involved. Goliath Cyber’s solution relies on all these datapoints while applying Machine Learning to create a baseline profile and determine deviations with a great degree of confidence. Potential activities, such as port scan, leading to a breach can be correlated in near-real time thus minimizing the scope and scale of breach, saving organizations from economic and reputation loss. Screenshot (aiSIEM Portal) of an alert below shows a particular host involved in data exfiltration.
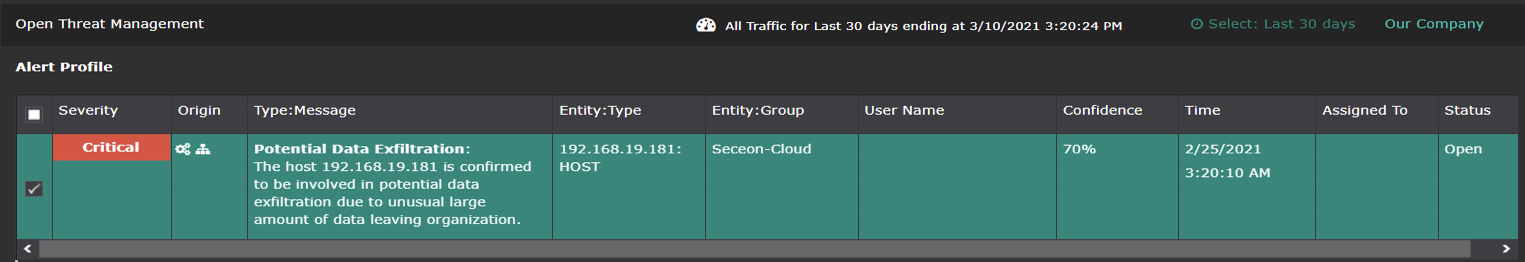
Upon peeking further into the underlying Threat Indicators, we find the host setting up a connection to another host (server) and application, exchanging communications (bytes) and, finally, uploading data to a public application.
Vulnerability Exploits
Adversaries look for vulnerabilities across digital assets to make inroads into an endpoint or server with the objective of planting malware, trojan, worms or bots. Also, at different stages of a malware’s evolution, there may attempts to conduct horizontal and vertical reconnaissance internally before beaconing with Command & Control Center. Establishing a communication channel with the C&C Center and exfiltrating data to a designated server becomes rather easy if vulnerabilities such as open port can be exploited.
Challenges
- Prioritization of vulnerabilities is often an arduous task, particularly with large organizations that may have hundreds and thousands.
- Remediating a security vulnerability can often take several weeks and months, given shortage of security staff amidst various work items.
- It is difficult to measure the success of a vulnerability management program since the outcome is intrinsic to continuous security and compliance.
Goliath Cyber’s Solution
With vulnerabilities being rampant across the IT environment, exploits have to be detected through various activities with a solid understanding of attacker’s tactics and techniques. Goliath Cyber’s solution analyzes various threat indicators to determine whether Vulnerability Exploit or Web Exploit should be flagged as a critical or major alert.
- Vulnerability Exploit usually involves IP Scan or Single Port Scan across the network, in an attempt to find servers with a particular open port. Subsequently, the malware could be connecting to the IRC Server in Public Domain.
- Web Exploit usually involves a blacklisted site attempting to get too much information through malformed url.
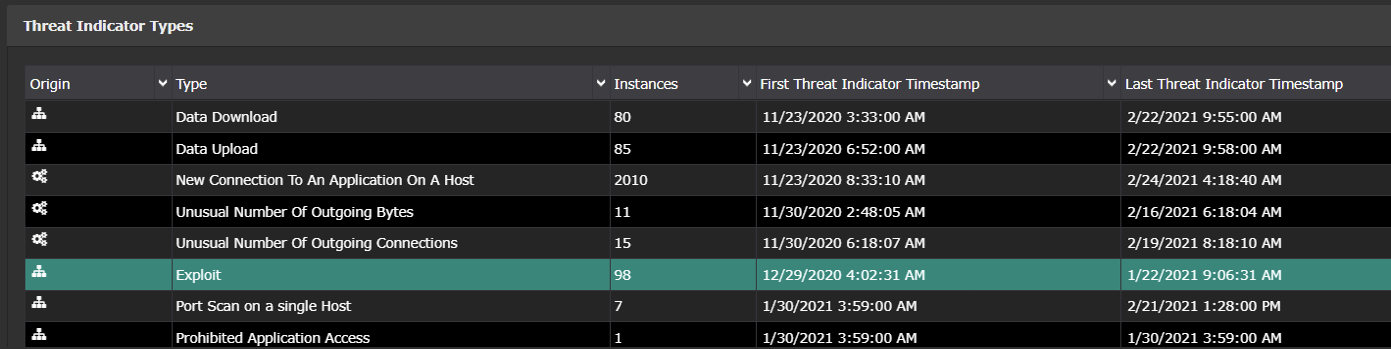
Screenshot (aiSIEM Portal) of a Vulnerability Exploit alert below shows a particular host conducting rigorous network scanning.
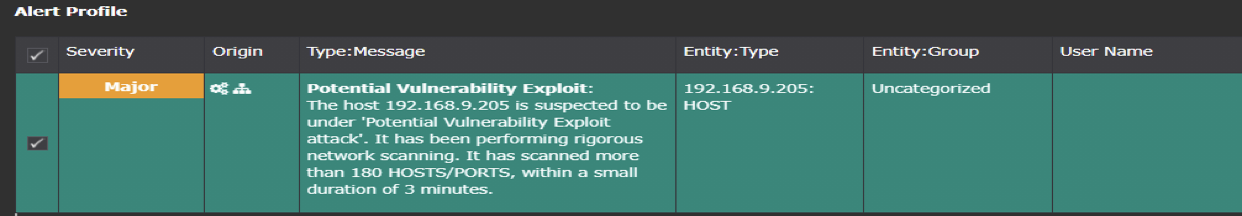
Upon peeking further into the underlying Threat Indicators, we find a slew of activities starting with port scan, prohibited application access, unusual outbound data, data download and upload. All these indicators are automatically generated by the OTM Platform using ML and AI.
Web Application Security
Web Applications are often created to in line with a special charter/mission, business objective or partner programs. However, proper coding guidelines and best practices are not followed consistently. Often, client-side code (javascript) may be used through browser plug-ins that is beyond the realm of control that enterprise security can enforce. Adversaries pry into web applications to access database, steal credentials, download malware or redirect user to malicious sites. Even worse, if they gain access to ERP, CRM and HRM systems that are front-ended with web interface. Some of the most troublesome cybersecurity attacks and breaches are instrumented through web applications, namely – Cross-Site Scripting, SQL Injection, Directory Traversal, Remote File Execution, Cross-Site Request Forgery and many more. (In 9 out 10 attacks, web applications can be compromised by hackers.)
Challenges
- Lack of website security knowledge within freelance web developers using standard tools like WordPress.
- High cost of tools to build layered defense – WAF, Vulnerability Scanners, Threat Detection and Remediation.
- Blind trust on applications and APIs serving out of IaaS, PaaS and SaaS in the Cloud, often used for data analytics and business processes.
Goliath Cyber’s Solution
As Web Applications continue to pose a major cyber security risk to organizations, Goliath Cyber’s solution (both aiSIEM and aiXDR) is capable of detecting various indicators of attack vectors categorized as event type “Web Exploits”.
- Cross-Site Scripting (XSS) Attack where text input field of a web application form is used by perpetrator to insert code that can redirect a user to a malicious website that is used to steal user’s cookies, session storage, personal data, credentials etc.
- SQL Injection Attack where an application expects text as input from a user in order to build a SQL query with string concatenation, thus allowing the perpetrator to modify attributes in the query
- Remote File Execution allows the perpetrator to take advantage of an application vulnerability that expects a file as input for a web page form field and does not properly sanitize it, thereby allowing a malicious script that may have be referencing a backdoor or webshell planted in the server.
- Local File Inclusion allows the perpetrator to upload a script (php) as a file in the body of the URL, so that the script – potentially a malicious webshell that was pre-planted – gets executed locally at the server.
- Directory Traversal is a dangerous move that an attacker can perform by taking advantage of Local File Inclusion vulnerability in the application and ultimately access user list, logs, source code etc.
Continuous Compliance
Compliance with regulatory statutes is a key component of an organization’s security posture. The purpose is to validate and align with the stipulated policies and regulatory requirements, attain proper attestation and avoid penalties.
Typically, obtaining an evidence of compliance has been a point-in-time activity. However, we need to be cognizant of However, potential deviation from compliance. What if an organization was compliant on Day 1 but drifted away on Day 10? Additionally, regulatory compliance is inherently vulnerable making it quite challenging for organizations to maintain a sound security posture and protect all the stakeholders. Hence, there is a dire need for an organization to be compliant at all times. Also, it is important for an organization to have the flexibility to easily evolve with the growing regulations and compliance laws.
Challenges
- Compliance laws are getting more stringent with strict penalties and large fines, while newer compliance laws are being introduced by governments, states and regions to enforce accountability on organizations and service providers dealing with personal data.
- Businesses are incurring huge capital expenditures, exhausting time and resources with staff dedicated to manage compliance.
- Lack of compliance inhibits organizations to grow and operate in different regions.
Goliath Cyber’s Solution
Compliance is observed across different areas of the aiSIEM and aiXDR products.
- Logs are stored in raw form with original timestamp and audit data, thus preserving the chain-of-custody, serving regulatory compliance and forensic needs.
- Multiple custom policies/rules for access (allow, limit, deny etc.) can be defined, correlated and stringently applied for security and compliance.
- User access to the aiSIEM and aiXDR Portal (GUI) is controlled via separate roles in order to limit privileges for security and compliance reasons.
- User activities are logged in the aiSIEM and aiXDR products for compliance and comprehensive audit.
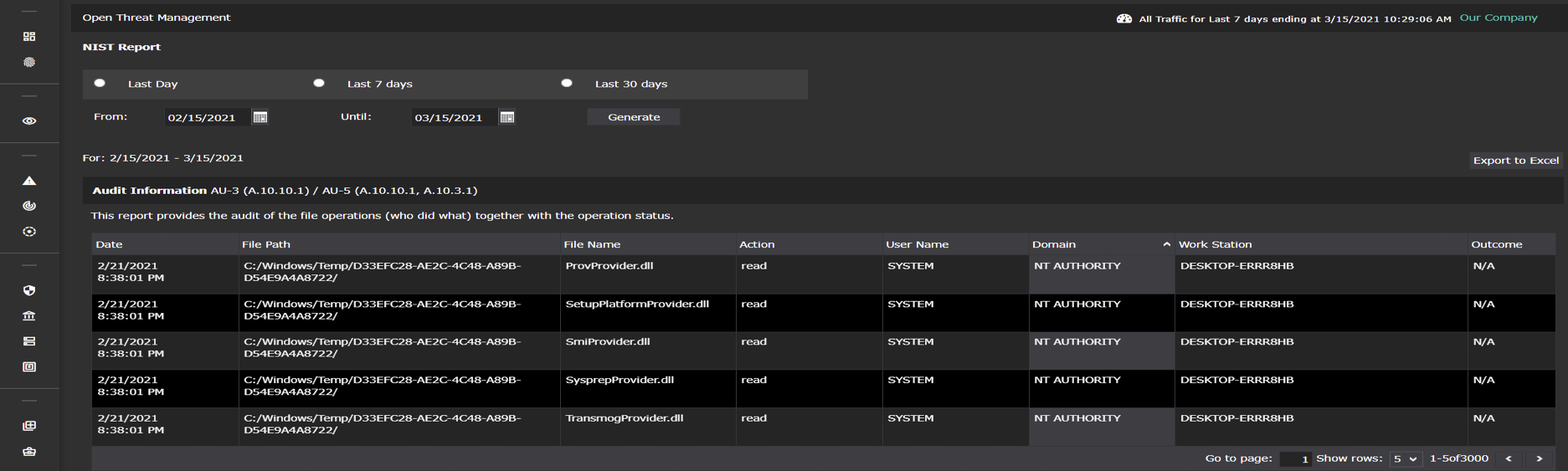
- Scheduled or on-demand reporting for HIPAA, PCI-DSS, NIST, GDPR and other regulatory requirements (see screenshot below for a sample NIST Report).
- Security Posture reports with graphical view of historical trend over a selected period provides an organization with extra immunity.
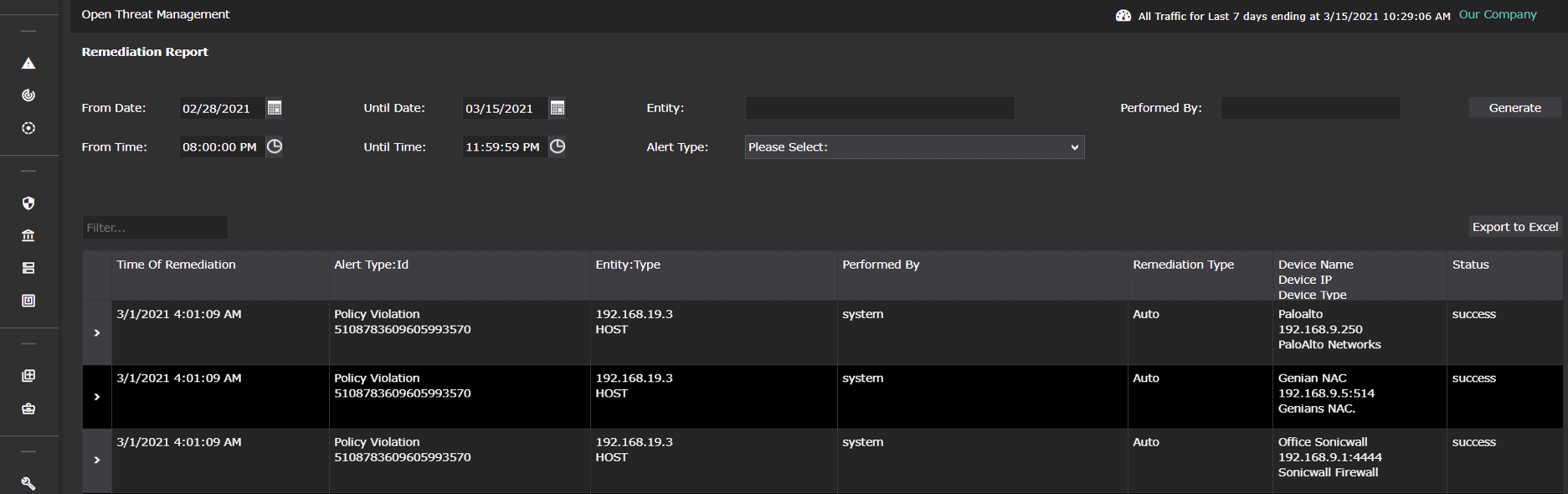
- Investigation reports (FTP Activity, SMTP Activity, Remediation Report) add on top of mandatory compliance requirements to furnish regulatory bodies (see screenshot below for a sample of Remediation Report).

Ransomeware Attack
Targeted ransomware attacks on government entities such as state departments, local (city / municipality) entities, schools, universities, enterprises, service providers and even small-medium businesses have seen a constant rise over the years. Much like the evolution of malware, Ransomware attacks have also evolved from basic type of attacks, usually limited to single host with some valuable data, to advanced attacks that are capable spreading across the network, aided by worms (ransomworm or cryptoworm) to increase hostages and monetary gains.
Often, ransomware (e.g Ryuk) are invoked through sophisticated trojans like Emotet that take evasive actions and even destroy backups, such as shadow files, on hosts/servers to maximize damage and prevent recovery through alternate means without payoff. Some of the well knows ransomware that have caused considerable damage are WannaCry, CryptoLocker, Ryuk, Petya, notPetya and Maze.
Challenges
Ransomware attack typically involves multiple stages and each stage can be usually detected as a suspicious threat indicator leading to a potential ransomware attack by different security products. However, the challenges with detecting and preventing the ransomware with the existing security tools is as follows:
- Increased number of false positives because of limited visibility of each security tool which most of the times results in alert fatigue.
- Mis-detection because of lack of advanced correlation across the multiple security tools.
- Delayed response because of more reliance on expert security analysts to correlate multiple suspicious activities in order to confirm the attack and then take action.
Goliath Cyber’s Solution
Detecting ransomware requires a high degree of reliance on behavioral analytics and threat modelling to follow various stages of its propagation. Traditional threat detection tools rely heavily on the security analyst to discern unusual activities and create correlation rules to stitch indicators together. This approach heavily weighs on the analyst’s skill in threat detection and fluency with a complex UI, thus leaving a factor of subjectivity in reaching the desired outcome. In sharp contrast, aiSIEM/aiXDR leans into Machine Learning for behavioral analytics and Artificial Intelligence for correlating indicators driven by built-in dynamic threat models. When these indicators line up with a certain degree of confidence, the algorithm raises an alert for the analyst to act upon.
Here are the top 3 scenarios corresponding to Ransomware detection with aiSIEM and aiXDR.
Detection at Host: The ransomware payload tries to make its way to the endpoint host. In the case of an attack based on email phishing, aiSIEM/aiXDR quickly swings into action, correlating logs from email server with endpoint activities to find traces of unusual or suspicious process spawned on the endpoint.
Detection at Host Connecting with C&C: The malware tries to establish connection with the Command and Control Center (C&C) from the affected host. It could potentially generate a new domain, programmatically and attempt connecting. During this stage, the aiSIEM/aiXDR platform steps in to detect the auto-generated domain names and correlate that information with other threat indicators to raise an alert.
Detection of Lateral Movement: Introduction of an infected host in the network could lead to a network scan conducted by the malware for the purposes of identifying potential target before propagating to other endpoints/servers like a worm. aiSIEM/aiXDR can detect this activity rapidly and correlate with contextual events to raise a “Potential Malware Infected Host” alert, followed by quarantining the infected host. (See adjacent image for activity flow)

DNS Protection
The Domain Name System (DNS) is the part of internet infrastructure that resolves easily remembered domain names that human’s use into more obscure IP addresses that internet- connected computers use.
The Challenge
Adversaries use DNS protocol to keep their communications covert and evade detection. In particular, malware use DNS to command and control channel and exfiltration to take advantage of the fact that DNS traffic is not analyzed by firewalls and IDS/IPS devices.
Goliath Cyber’s Solution
Through deep packet analysis of DNS traffic, Goliath Cyber’s solution (aiXDR and aiSIEM) is able to identify protocol abuses and analyze behavioral changes related to DNS Tunneling. Goliath Cyber’s Threat Intelligence (STI), feeding in from more than 70 sources, is effectively used to identify blacklisted domains and URLs. In addition, the solution comes integrated with APIs of many Firewalls to automatically push policies aimed at blocking communication with blacklisted domains, C&C communications etc.
Here are some features/functionalities that combine to form DNS Protection.
- Secures DNS infrastructure by identifying DDoS Amplification Attacks and Volumetric Attacks on the infrastructure and raising alerts.
- Uses Artificial Algorithms to identify DDoS Attacks and C&C communications.
- Identifies suspicious and domains by Proactively detects domains generated using DGA algorithms.
- Performs Real time DNS traffic inspection (Deep packet Inspection) to identify threats.
- Analyzes DNS queries and responses in real time to derive insights such as increase in number of failures.
- Leverages Network Behavior Analytics to detect traffic pattern changes (such as DNS packets/sec, DNS flows/sec etc) that can lead to Advanced Persistent Threats (APT)
Detects DN Changer trojan.
Cloud Asset Monitoring
Key business applications, databases, productivity suites and various type of structured/unstructured data reside in the Cloud today for a vast majority of businesses and enterprises. Hence proper visibility into events and activities in the cloud is crucial for ensuring sound security posture. Cloud VMs, data analytics, business applications and data repositories may be accessed by different types of users, internal and external (Partners, Supplier, Distributors etc), thereby increasing the risk of compromised credential, lateral movement and data breach. Additionally, IIOT and IT-OT data is predominantly streamed into data lake in the cloud for analysis, visualization and decision-oriented measures, increasing the threat surface area.
What about the web applications served from the cloud? Aren’t those vulnerable to web exploits potentially resulting in malicious intrusion, backdoors (webshell) and eventually, data breach?
All these scenarios point to the most fundamental premise of cloud security – to be able to monitor assets in the cloud for enhanced visibility and threat detection.
Challenges
- Securing assets in the cloud is a continuous process, in keeping with the growing transactions, touch-points and realm of an organization and its associated products/services. While a maturity model may establish a stepped, structured approach to readiness, for most part gaps are evident from a dearth of understanding and appropriate action.
- Applying the notion of “least privilege”, to limit user access within applications and asset in the cloud, is made difficult by the redesign involved
- Leap to the cloud is propelled by business decisions (Capex to Opex, On-demand Availability, Time-to-Market, Ease-of-Maintenance etc), often bypassing existence of potential threats and consequences
- Laying out defense-in-depth measures is crucial for cloud but the lack of a comprehensive solution makes it prone to gaps, with the alternative being costly investment
- For the most part, Cloud Security products talk about prevention, whereas robust alerting system for incident response goes a long way towards damage control
- Credential stuffing with weak or stolen credentials can lead to account compromise and eventually data breaches and service disruptions in the cloud
Goliath Cyber’s Solutions
Goliath Cyber realizes the significance of monitoring cloud based assets in ensuring well being of an organization. Hence visibility is gained through events, network flows (via firewalls), threat intelligence, IDS/IPS and EDR – all amalgamated in a unified user interface with seamless navigation. Threat Indicators (TI) are then created for suspicious connections, data transfers (VMs with cloud and outside), port scan (horizontal and vertical), unusual user access, trojan-like behavior and various other behavioral anomalies, based on established patterns. Depending on the nature of threat indicators in the mix and the no. of instances over a period of time, particular type of events may be raised.
Here is a subset of security events (threat types) that are handled by the aiXDR and aiSIEM platform across servers and applications running in the cloud.
- Compromised Credential
- Brute-Force Attack
- Blacklisted Site Access
- SQL Injection
- Potential Ransomware
- Zero-Day Malware
- DDoS Attacks
- Trojan Activity
- Cross-site Scripting
- DNS Tunneling Attack
Goliath Cyber – aiXDR Platform
Built from the ground up with NATIVELY integrated capabilities of the components from theSOC visibility triad, it is offered as a SINGLE license platform, with every component contained in the image you see below!